# Request validation for Web Apps
The purpose of this report is to expose the information of different website protection tools, and try to evaluate which of them is useful for each situation.
# CSRF
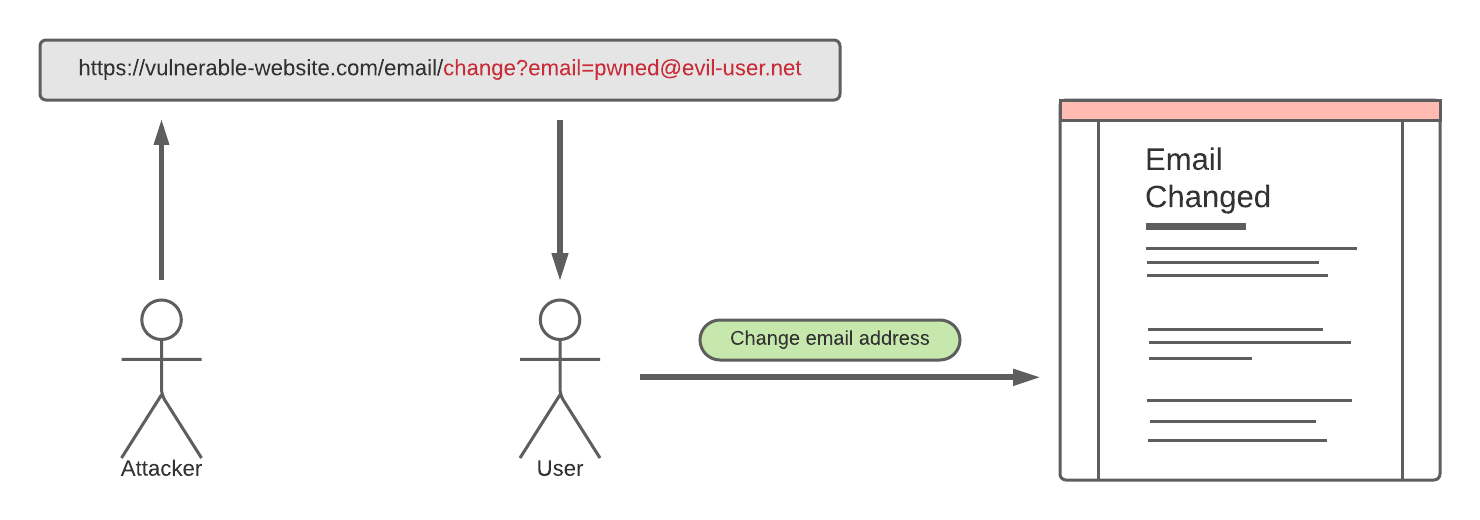
CSRF (Cross-site request forgery) vulnerabilities allows an attacker to induce users to perform actions that they do not intend to perform.
# Prevent CSRF attacks
In order to prevent CSRF attacks, there are different ways. The most common and simple is to use a non-cookie-based session handler for tracking user sessions or validating requests. Although, the most secure way to prevent this attacks is to use a CSRF token to validate at least the relevant requests (modification of user data/permissions).
# CSRF Tokens
A CSRF Token is a unique, secret and unpredictable value that is generated in the server-side and sent to the client in such a way that it is included in a subsequent HTTP request made by the client. It is recommendable to link the token to the user session, so that it can be validated together with the user session token. In order to transmit a CSRF Token, there are different ways:
- The Token can be transmitted by a POST method (i.e. when the user logs in) via hidden input field
<input type="hidden" name="csrf-token" value="CIwNZNlR4XbisJF39I8yWnWX9wX4WFoz"/>
- The Token can be transmited within a custom request header (Which is the case of the ImageUploader Application built in previous assignments). This is a strong defense against attackers because browsers do not normally allow custom headers to be sent cross-domain.
# How CSURF works
CSURF is a Node.js module that can generate, transmit and validate CSRF tokens in the server-side.
# Client -- Server communication
On a first GET request, the server sends the client two cookies, with the names of _csrf and XSRF-TOKEN
_csrfis generated automatically when{ cookie: true }option is set.
var csrf = require('csurf');
var csrfProtection = csrf({ cookie: true });
2
This is a secret, not the CSRF token. The server uses this secret to match the actual token against it. The
_csrfcookie is an alternative to using sessions. Instead of storing the secret on the server, tied to a user session, it is stored on the client’s browser as a cookie
XSRF-TOKENis the current CSRF token. It is generated viareq.csrfToken()function. It is recommended to be sent to the client on the first request (GET). This can be done in multiple ways; the example project sets it as a cookie. The client needs to send it back either in the body, query string, or headers of every request
# CSRF Token validation
For every following GET request:
- CSRF protection is not necessary.
The
csrfProtectionmiddleware should not be used on the server code for any GET endpoint other than the first one
For every following POST/PATCH/PUT/DELETE request:
- The use the
csrfProtectionmiddleware on the server is mandatory, unless the route has not access to critical data or can communicate with other route that has access to that kind of information
The server will check the
_csrfcookie sent by the client against the value ofXSRF-TOKEN, sent also by the client, in the request body, query string, or headers
# Considerations
- The
XSRF-TOKENwill probably be sent back by the client as a cookie for this example, but the server will ignore it, as it will look for it only in the headers. - The code that generates the token (
res.cookie('XSRF-TOKEN', req.csrfToken())) should only be run once - The
_csrfsecret is generated by the server every time the client sends a request that does not include the_csrfcookie and hits a route that uses thecsrfProtectionmiddleware - When using the
csrfProtectionon aGETroute, the server will ignore any CSRF check. However, it will generate and set a new secret cookie,_csrfif the client did not send it
# JWT
JSON Web Token is an open standard that defines a compact and self-contained way for securely transmitting information between parties as a JSON object.
# When to use JWT?
Authorization: Common scenario. Once the user is logged in, each subsequent request sill include the JWT, allowing the user to access routes, services and resources permitted with that token (Roles).
Single Sign On (SSO)
# JWT as a CSRF Token
The key properties of a CSRF token are that it is not predictable by an attacker, and, unlike cookies, it is not added to every request by the browser. A cryptographically secure JWT stored in a hidden field meets both of these properties, because JWT has to store user-unique data in it to be secure. It is recommended to use an external CSRF Token generator together with a session token generator like JWT to increase security.
The example app show how CSRF Tokens can be used together with a session token.
# Passport.js
Passport is authentication middleware for Node.js.
# Passport features
Passport has basically the same features as JWT, but the difference is that Passport provides different middlewares in order to facilitate the use of features like OAuth 2.0, and it is easy to have a secure server running in a few minutes.
# Passport with CSRF Tokens
The way to use Passport together with a CSRF Token generator is the same as it is done using JWT.